In a world where data security has become a superstar and workplace security a stumbling block, there's a new sheriff in town - the ISGUS security monitor. Forget everything you know about boring security solutions because this monitor is the true rockstar in the world of corporate security. Companies not only need to protect their physical premises and employees, but also digital data and information from cyberattacks. These challenges require integrated solutions that take a holistic approach to security.
ISGUS, a leading Workforce Management company, has taken on this challenge. With decades of experience in developing solutions for Time and Attendance and Access Control, ISGUS has expanded its know-how into the area of corporate security. The ISGUS security monitor is a result of these efforts.
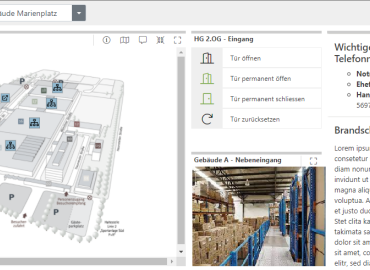
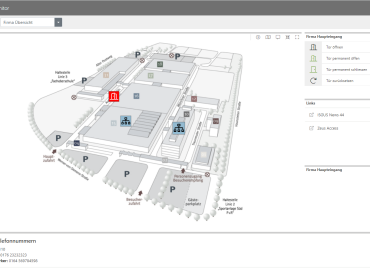
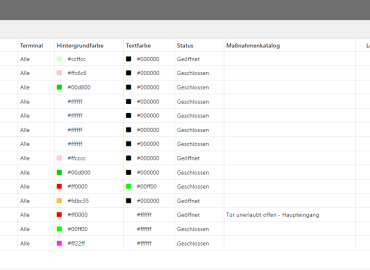
Our security monitor is a comprehensive solution for workplace safety. It offers a wide range of features to help companies achieve their security goals. The security monitor visualizes and manages all events and messages that are generated and forwarded by the ZEUS® Access Control. This means your security officers can easily monitor all protected areas. These can be clearly compiled on any dashboard and accessed by the security department. All conceivable access events can be categorized and reactions or actions can be defined for each type of event.
The ISGUS security monitor is a milestone in corporate security. In a time where data thieves and security breaches are commonplace, the ISGUS security monitor is your best ally. It won't let you down, protects your team and your values, and ensures your company navigates the security jungle like a rock star.
The ZEUS® security monitor complements your access control!
To further increase security, the security monitor offers a visual representation and management of all events and messages that are generated and transmitted by the ZEUS® access control system. This means your representatives can easily monitor all protected areas. This data can be clearly compiled on various dashboards and accessed by your security department. It is also possible to divide all conceivable access experiences into categories and to define reactions or actions for each type of event.